In October 2015, Google made algorithm changes to target hacked websites and affected 5% of queries. You can't help but worry the moment you realize that your website has been hacked. However, remember that yours is one among hundreds of websites that get infected with viruses and malware all the time. The good news is that the following article on hacked websites has you covered. I'll go through the basics to help restore your website and its controls.
Table of Contents
How Did Your Website Get Hacked?
Cyber criminals usually find vulnerable spots in your website and take advantage of it by introducing malware or viruses. For instance, you may install a plug-in to your website that unbeknownst to you has a vulnerability cyber criminals can capitalize on. Then, the attackers create a virus and release it to the Internet. This virus hunts for websites that have this plug-in installed and hack them.
Most people doesn't realize their websites are hacked until Google indicates such in its search results. Alternatively, you might get an email from Google warning that your website may be hacked. Keep in mind that hackers can steal your log-in credentials as well as those who visit your website. With this data, they can steal from you and your visitors. Any warning that your site is hacked warrants immediate attention.
Step-By-Step Guide for Hacked Websites
You'll need to have some technical knowledge to get hacked websites up and running again. If you don't, I recommend that you consult with the experts out there. Nevertheless, I urge you to go through the following steps to disinfect your website.
1. Put a Support Team in Place
The first thing to do is inform your host. Most of the hosts are forthcoming with help in situations of hacked websites. Another great idea is to look for help online. You could post your problem and discuss it in a forum. Ask for recommendations from your friends for an expert. You may want to hire members of online forums who seem to have expertise on the subject.
Some places online I suggest are:
- Stop Badware: This website has a community forum, articles, and tools for help with infected and hacked websites.
- Google Webmaster Central: A sub-forum here is dedicated to tackling hacking issues.
2. Quarantine Your Hacked Website
Next, you'll need to quarantine your website so that no one else is infected. You must take your website offline for this. Here you’ll direct your DNS entries to a static page through a “different server” that uses HTTP 503 response. By doing this, you are limiting the access of your hacker.
If you are worried about your SEO ranking being dropped, you can breathe free because being temporarily down won't have an effect. Get in touch with your host for suggestions to achieve this. It's possible your host is encountering a similar situation and will be very understanding.
Remember that the following steps are insufficient:
- Use of robot.txt disallow
- Getting your own website to display a 404 or 503 error
It’s time for in-depth account management. Go through all the user accounts. The hacker might have created their own user accounts. If so, note these down so that you can investigate them further later. Now, delete such accounts. Change passwords for all sites and accounts. You'll also need to look into:
- Content management accounts
- FTP logins
- System admins
- Database access
3. Verify Ownership with the Search Console
If you don't have verified ownership of your website, you’ll have to perform this step. Begin by signing into the Search Console on Webmaster Central using your Google account. Click on “add a site” and then “continue.” You'll be presented with options for verification. You’ll find “recommended” methods and also the “alternate” method. Choose whichever is most convenient to you.
Once you accomplish this, bring your website back online if the verification method you chose warrants you to do so. Some methods require access to your HTML file or HTML meta tag. Then, click verify. Immediately after you receive confirmation of verification, make the website offline again.
Now that you’re verified, check whether the hacker previously verified ownership in Search Console and made any changes in the settings. To do this, go to the homepage and click on manage site. Click on add/remove users. Make certain that you recognize all the owners and users listed there.
If you find an unauthorized user, note down the email address first for future investigation and delete them. Take every precaution to ensure the unauthorized owner doesn't create an account again. Remove verification tokens like the verification meta tag on HTML file on your server or meta tag on the homepage.
Look for any change in settings that have been made and restore them. Go through the Google Index and review the “gear icon,” “remove URL,” and “change address” to see if there’s anything amiss.
Know Your Attack: Cyber criminals attack hacked websites for various reasons, including:
- Phishing
- Uploading spammy content
- Malware distribution
Find out the nature of your attack by going to the Search Console homepage and clicking on messages. Look for a message from Google regarding the nature of attack. If you find one, don't delete it until the entire recovery process is over.
Next, go to “Security Issues” in Webmaster Tools. Owners of hacked websites will see a top-level heading that reads one of the following:
Malware: Under this heading will be the kind of malware that has been infused into your website.
Hacked: This means the website was hacked to introduce spammy text or links.
Phishing: This means the hacker was trying to steal login credentials from you and your visitors.
4. Assessing the Damage
There could be two types of damage: spam or malware. If your Google search results display the message “This site may be hacked,” it means that your website may be distributing spammy content. Cleansing hacked websites is a lengthy process I will discuss later. However, if the Google search results show the message “This site may harm your computer,” here's what you need to do.
Precautions:
- Avoid using a browser to view pages on your website.
- Record details, such as name and location of damaged files, for later use.
- Make use of Wget or cURL for any HTTP requests.
Know the malware: Choose your verified website in Search Console and go to “Security Issues.” As mentioned earlier, you’ll see the type of infection here. Make note of all the information displayed about the malware by clicking on “Show Details.” We'll use this information later, so document thoroughly.
Assess the file-system damage: The hacker might have created entirely new pages or left backdoors for his reentry. If your site is online, make it offline and:
- Zero down on the files created/modified since the last backup. Take note of these files for later investigation.
- Check the server, error logs, and access for any activity that seems out of the ordinary. Look for unknown user accounts and failed log-in attempts.
- Review the configuration files, such as httpd.conf and .htaccess.
- Look for any lenient file or folder permissions.
- If you are in possession of a database, analyze each and every record making use of a tool like phpMyAdmin.
5. Identify Vulnerabilities
Many hacked websites use vulnerability scanners in this step. However, ensure that you have a backup of your website as these scanners can cause extra damage. They are completely different from and more invasive than usual antivirus scanners.
- If you choose to do it manually, check for the following aspects:
- Is the administrator’s computer infected with virus?
- Have you been using weak passwords?
- Is the software out of date?
- Have you been using permissive coding practices? (i.e. SQL injections and open redirects)
6. Clean Up Your Website!
Hacked websites often have confidential information that was compromised. If that's the case, the first thing to do is consult with a legal expert. Read useful resources provided by organizations like the Anti-Phishing Working Group too.
Remove any URLs that were created by the hacker. You can delete the page and give out an 404 error status. Or, you can remove the pages from Google search results by utilizing the tool Remove URL.
You may want ask Google to re-crawl your clean pages. Make use of Fetch as Google through Search Console. Ignoring this step is fine though because Google will re-index the pages in time anyway.
Start cleaning your server: This can be an extensive step for many hacked websites depending on whether they have backup or not. Let's explore the three distinct possibilities here:
- You have a current and clean backup: You’re lucky! Simply restore the backup. Install any upgrades, updates, etc. Remove any unnecessary widgets and plug-ins. Correct the vulnerability that led to the hacker attack. Remember the notes you had taken in step 4 where you assessed damage? Now is the time to address them. Change all passwords one final time.
- You have a clean but not current backup: For safety's sake, first make a disk image of your website although it’s still infected. Backup your server’s file system. This could include media, images, and databases. Then, restore the clean but outdated backup available with you. Consider removing any unwanted or unused widgets, plug-ins, etc. and performing upgrades.Hacked websites must correct the vulnerability that led to the attack. Conduct an automated or manual site “diff”. If there’s any clean content that was previously infected and you feel it’s valuable, upload it. Remember the notes you had taken in step 4 where you assessed damage? Now is the time to address them. Change all passwords one final time.
- No backup: Hacked websites in this category shouldn't panic. Make two backups of your infected website, one of which will be a clone version or disk image. In case you don’t have that, make two backups of file system as well as database. Clean the content of the site on a file system. Remember, the cleaning is not to be done on the server itself. If there were too lenient file systems, rectify that problem. Again, that’s to be done on backup copy and not on the server.
Remember the notes you had taken in step 4 where you assessed damage? Now is the time to address them. Remove all the files that were put in place by the hacker. Correct the vulnerability in your codes or password that was cracked. If there’s a database in your site, clean it and double check that it’s unsoiled. Change all passwords one final time.
Congratulations! Your hacked websites are now clean. But, you'll need to implement a maintenance plan so that you’re not caught in a similar situation in the future. This article by Stop Badware is a good place to start gaining knowledge on the subject. In general, make sure that you:
- Keep software updated.
- Always go for strong passwords.
- Make regular automated backups.
- Understand the security vulnerability for plug-ins or applications and pick only reliable ones.
Now you can bring your website back online!
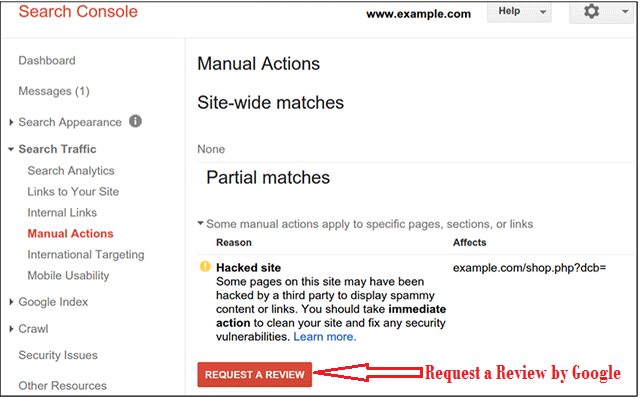
7. Request a Review by Google
If you’re confident that your website has fully reversed damage caused by the hacker, request a review from Google. This will help remove the warnings of hacked websites in the search results. Google will be looking for an extensive explanation about all the steps that were taken to rectify the situation. Take time to explain your efforts put on the work.
In case you fail the review, Google results will display more of your infected pages with warnings on the search results. This action is aimed at assisting you with disinfection and also warning vulnerable visitors.
Review times: Google takes about a day to complete reviews on hacked websites when there was a problem with malware. However, if the issue was with spam, the review may take several weeks. Once the review is complete, Google takes about 24 hours to remove the warnings on search results.
Case Study: Hacking Can Result in Negative SEO and Penalties Manually
According to a case study published in Link Research Tools, hacked websites can be penalized manually by Google. A hacking attack on a university website resulted in negative SEO even though the website itself was a victim. However, there's some good news. In this case, it took Google only one request to crawl the website back up once it was disinfected.
The Final Word
Hacking is never a pleasant experience. It can leave hacked websites out of action for several weeks, thus affecting your online traffic and revenue. There's always a solution hacked websites can take, even though they can be quite extensive. Rather than look for a cure later, focus your energy on prevention. Follow the security measures listed above to relieve your fears of crippling attacks.
If you’ve been a victim of hacking and are reeling under the burden of disinfecting your website, I'm happy to help. Reach out through the comment section below.



![20 best seo chrome extensions that you need to know in [year] 11 best seo chrome extensions that you need to know](https://shanebarker.com/wp-content/uploads/2021/09/seo-chrome-extensions.jpeg)



Seriously, strong passwords are a must. I’m constantly helping my family/friends get rid of viruses, and their passwords are usually something as simple as a name of a friend, or their birthday, or oftentimes, just Password. It’s really ridiculous, honestly.
The issue is that most people don’t think about the strength of a password until they get hacked. Be pro-active, not reactive.
Yes, I agree with Shane, and also thanks for the great article. Passwords are important but keeping your website updated is vital as well.